An analysis of Twitter’s screwup (with comments from Melissa Agnes)
 Twitter screwed up and wrote everybody’s passwords to a file in plaintext. Then (of course) they apologized. Can we do better with these apologies? And what’s the fallout from this incident? Here’s an analysis and a conversation with Crisis Communication expert Melissa Agnes, author of Crisis Ready.
Twitter screwed up and wrote everybody’s passwords to a file in plaintext. Then (of course) they apologized. Can we do better with these apologies? And what’s the fallout from this incident? Here’s an analysis and a conversation with Crisis Communication expert Melissa Agnes, author of Crisis Ready.
This is getting routine. And that’s the problem.
At this point, it’s obvious even to non-security experts like me that no vendor should post user passwords in plaintext, ever, anywhere. This is pretty close to the first principle of data security. And Twitter is not some tiny vendor. So this is a shocking development.
To be clear, there is no evidence that anyone outside Twitter saw or read this file. But they could have — an unscrupulous person inside Twitter could have sold it to hackers for a quick couple of million dollars, I’d guess. So that’s not particularly reassuring.
Let’s take a look at Twitter’s message to users about the problem. The additional comments are mine.
When you set a password for your Twitter account, we use technology that masks it so no one at the company can see it. We recently identified a bug that stored passwords unmasked in an internal log. We have fixed the bug, and our investigation shows no indication of breach or misuse by anyone.
Commentary: Gets points for clarity, getting to the point, use of “we” and “you,” and active voice. In the first paragraph we get an explanation of hashed versus plaintext passwords (not so easy to explain to lay people quickly), what went wrong, and the fact that they have no evidence the passwords leaked out. But “we recently identified a bug” is not the same as “we made a mistake.” A bug is a mistake made by a coder. Twitter made a mistake, and calling it a bug is evading responsibility.
Translation: We stored your Twitter password in plain text in a log on our site. Oops. We don’t think anyone saw it.
Out of an abundance of caution, we ask that you consider changing your password on all services where you’ve used this password. You can change your Twitter password anytime by going to the password settings page.
Commentary: This starts with a self-contradictory sentence. “Out of an abundance of caution” makes it sound like this is not a big deal. “We ask that you consider” is a similarly weak construction. But they’re not so confident that they would tell you to do nothing.
Translation: It’s probably nothing, but there’s a chance that hackers are exploiting your password that we stored in plain text on our server. So, change it everywhere you use it. Like on your bank account — I’d definitely change that one.
About The Bug
We mask passwords through a process called hashing using a function known as bcrypt, which replaces the actual password with a random set of numbers and letters that are stored in Twitter’s system. This allows our systems to validate your account credentials without revealing your password. This is an industry standard.
Due to a bug, passwords were written to an internal log before completing the hashing process. We found this error ourselves, removed the passwords, and are implementing plans to prevent this bug from happening again.
Commentary: This is a decent explanation of hashing. But I don’t think those letters and numbers are random.
Tips on Account Security
Again, although we have no reason to believe password information ever left Twitter’s systems or was misused by anyone, there are a few steps you can take to help us keep your account safe:
- Change your password on Twitter and on any other service where you may have used the same password.
- Use a strong password that you don’t reuse on other websites.
- Enable login verification, also known as two factor authentication. This is the single best action you can take to increase your account security.
- Use a password manager to make sure you’re using strong, unique passwords everywhere.
Commentary: A straightforward set of instructions.
We are very sorry this happened. We recognize and appreciate the trust you place in us, and are committed to earning that trust every day.
Commentary: I’d be happier if the apology were at the end. And the platitudes don’t reassure me at all.
Translation: Oops. Sorry. It’s only your password, after all. We’ll do a better job in the future.
A conversation with Melissa Agnes about this incident
I reached crisis communications expert Melissa Agnes for a Facebook chat about this. Here’s what we said:
Josh: Good morning! So, Melissa, we wake up and see that Twitter has shared all out passwords. What was your first impression?
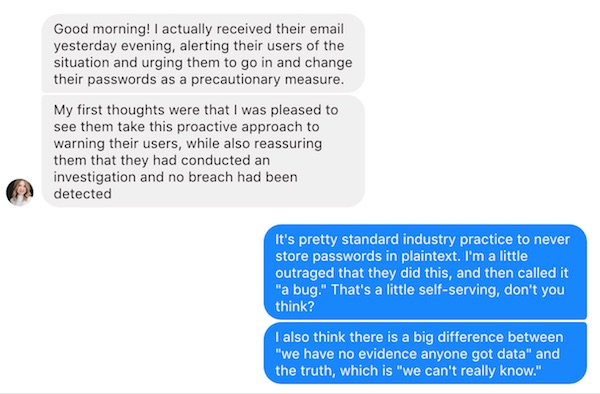
Melissa: Good morning! I actually received their email yesterday evening, alerting their users of the situation and urging them to go in and change their passwords as a precautionary measure.
My first thoughts were that I was pleased to see them take this proactive approach to warning their users, while also reassuring them that they had conducted an investigation and no breach had been detected
Josh: It’s pretty standard industry practice to never store passwords in plaintext. I’m a little outraged that they did this, and then called it “a bug.” That’s a little self-serving, don’t you think?
I also think there is a big difference between “we have no evidence anyone got data” and the truth, which is “we can’t really know.”
Melissa: The truth is they can’t really know, you’re right. But “we have no evidence” demonstrates that they’ve taken measures to investigate. Which answers anticipated questions by users and the media.
It shows that they were proactive here too – and communicates a message of prioritizing the situation, as it should have been.
Melissa: From my understanding, the plaintext was not intentional. That is what they’re communicating anyway.
Josh: Of course it was not intentional. But it was a mistake. Calling it a “bug” makes it sound like they’re not responsible, when of course they are.You see lots of these breach announcements and have written about them in your book. What do you think is the broader impact on consumers’ attitudes from seeing all these. Are they jaded and resigned? How does this change the comms strategy?
Melissa: It’s a scary thing when the general public becomes desensitized to the security of their personally identifiable information (PII), but this is what we’re seeing as a result of all of the major breaches of the past few years.Twitter is the least of our worries, in comparison to Equifax, Anthem, Sony, Home Depot, etc.
Josh: Soooo reassuring!
Melissa: In regard to the language of “bug”, this is actually a strategic term and I think it works well.
It uses terminology that everyone understands.
Melissa: While mitigating their legal department’s hesitations or push-back.
This is true. But as a crisis management strategist, I have to look at all the angles.
On a high-level, I think Twitter did the right thing in their proactive communications and actions.
However, I agree with you whole-heartedly, this should have happened in the first place.Today’s organizations have a deep responsibility in protecting the data they are entrusted with.
Josh: One last question for you. I’m sure you’ve never before had the challenge of writing in a chat and having it published right afterwards. How does it feel to know your every word will go out right after you say it?

Josh: Yeah, but I have no filter and they do! Thanks for playing along.
Melissa: I love that about you, Mr. Without Bullshit!
I rented a U-Haul 8 foot open trailer last weekend. For the very first time ever (the rep told me this is a new procedure started two weeks ago) they took a picture of the front and back of my driver’s license. I ask the U-Haul attendant how well he was going to protect my PII. He claimed very well. At the time I had no alternatives so I complied. Should I believe that U-Haul, not really a tech company, can protect this data better than Equafax or Twitter or …? That will likely be the last time I rent from U-Haul. Even more amazing to me is U-Haul’s insensitivity to my concerns around gathering and storing this type of information. I can only imagine that they will never expand to Europe.
U-Haul, as you know, is a transportation company. It isn’t a tech company. Even tech-focused companies, obviously, have difficulty keeping users/customers PII secure. You’re right to be concerned that a company whose primary function isn’t oriented to keeping your PII secure would be well able to do so. That said, given that quite a number of terrorist attacks in the US have been carried out with rental trucks, I can understand why the company might need to keep a well-documented record of who rented their vehicles. They may be between a proverbial rock (government demands) and a hard place (having to muddle through to keep your collected PII safe).
Thanks for the warning! I was going to rent a U-Haul trailer in a few weeks. I’ll try Penske instead, and hope they aren’t also so careless with my concerns.